Configuring Dynamic NAT on Cisco Routers
Welcome to another tutorial on Network Address Translation (NAT). In this post we'll be looking at how to configure Dynamic NAT on Cisco routers. I highly recommend that you first read through my previous post on configuring static NAT before continuing with this one.
What is Dynamic NAT?
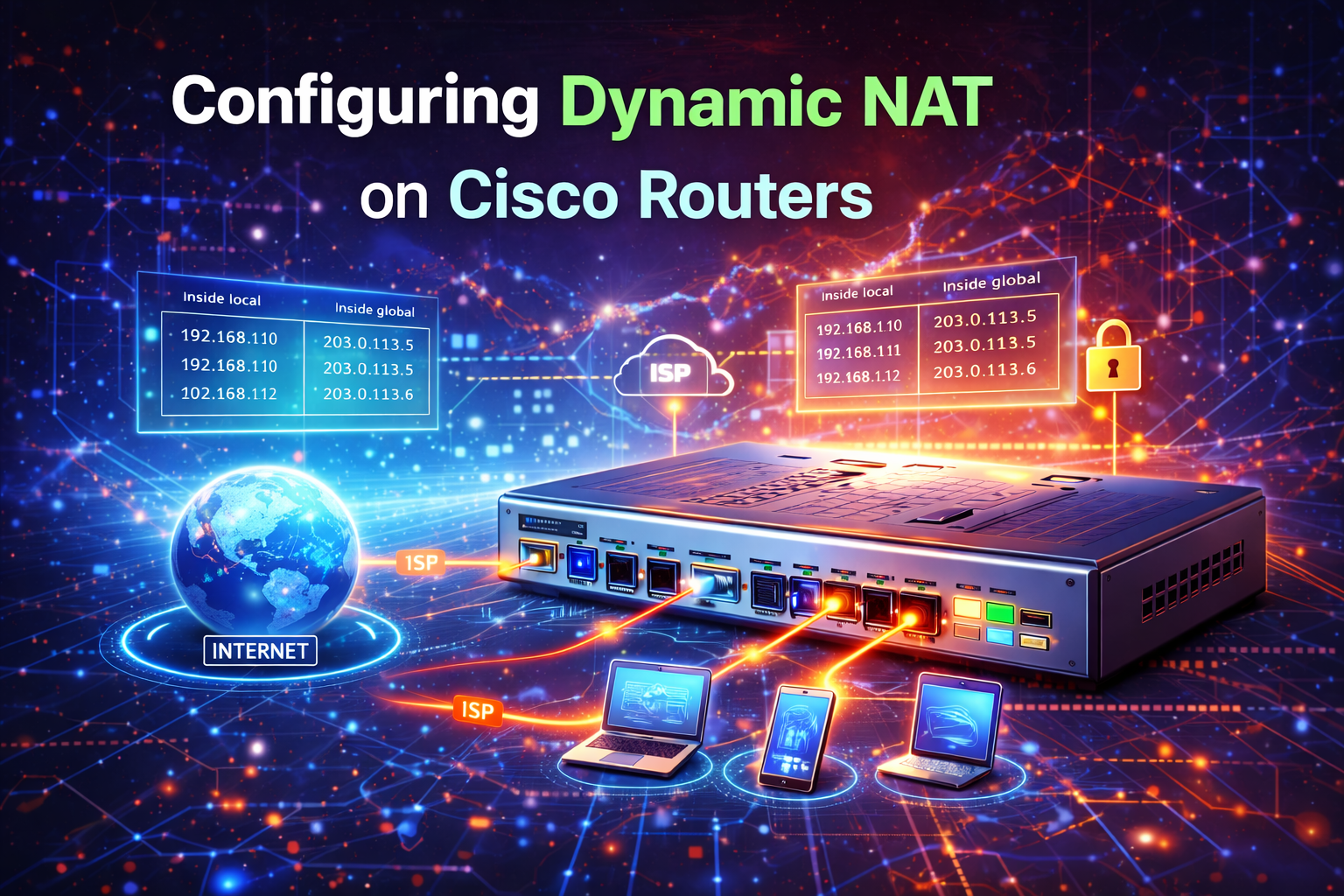
Dynamic NAT is similar to static NAT in that it creates a one-to-one mapping between a private IP address and a public IP address. The difference is that with dynamic NAT, the mappings are created dynamically as traffic flows through the router, rather than being configured manually like with static NAT.
Dynamic NAT requires a pool of public IP addresses to work with. When a host on the inside network initiates a connection to a host on the outside network, the router will automatically assign one of the available public IP addresses from the pool to that inside host for the duration of the session.
When to Use Dynamic NAT
Dynamic NAT is useful when:
- You have a limited number of public IP addresses but more internal hosts than public IPs
- Not all internal hosts need to access the internet simultaneously
- You don't need permanent mappings (like you would with servers)
- You want to conserve public IP address space
Dynamic NAT Configuration
Let's look at the configuration steps for dynamic NAT:
Step 1: Define Inside and Outside Interfaces
First, we need to define which interfaces are inside and which are outside:
Router(config)# interface GigabitEthernet0/0
Router(config-if)# ip nat outside
Router(config-if)# exit
Router(config)# interface GigabitEthernet0/1
Router(config-if)# ip nat inside
Router(config-if)# exitStep 2: Create an Access Control List
We need to create an ACL to define which inside addresses are allowed to be translated:
Router(config)# access-list 1 permit 192.168.1.0 0.0.0.255This ACL permits all hosts on the 192.168.1.0/24 network to be translated.
Step 3: Define the NAT Pool
Next, we create a pool of public IP addresses that will be used for translation:
Router(config)# ip nat pool PUBLIC_POOL 203.0.113.10 203.0.113.20 netmask 255.255.255.0This creates a pool named PUBLIC_POOL with public IP addresses ranging from 203.0.113.10 to 203.0.113.20.
Step 4: Configure the NAT Translation
Finally, we tie everything together with the NAT translation command:
Router(config)# ip nat inside source list 1 pool PUBLIC_POOLThis command tells the router to translate addresses that match ACL 1 using IP addresses from the PUBLIC_POOL.
Complete Configuration Example
Here's the complete configuration for our dynamic NAT setup:
! Define inside and outside interfaces
interface GigabitEthernet0/0
ip address 203.0.113.1 255.255.255.0
ip nat outside
no shutdown
interface GigabitEthernet0/1
ip address 192.168.1.1 255.255.255.0
ip nat inside
no shutdown
! Create ACL to define inside addresses
access-list 1 permit 192.168.1.0 0.0.0.255
! Define NAT pool
ip nat pool PUBLIC_POOL 203.0.113.10 203.0.113.20 netmask 255.255.255.0
! Configure NAT translation
ip nat inside source list 1 pool PUBLIC_POOLVerification Commands
Use these commands to verify your dynamic NAT configuration:
Show NAT Translations
Router# show ip nat translationsThis displays all active NAT translations. For dynamic NAT, you'll only see entries when there are active connections.
Show NAT Statistics
Router# show ip nat statisticsThis shows detailed NAT statistics including:
- Number of active translations
- Number of hits
- Number of misses
- Pool information
Clear NAT Translations
To clear all dynamic NAT translations:
Router# clear ip nat translation *Troubleshooting Dynamic NAT
Common issues and solutions:
No Available Addresses in Pool
If you see this error message: %NAT: translation failed (pool exhausted), it means all IP addresses in your NAT pool are currently in use. You can:
- Add more IP addresses to the pool
- Reduce the NAT translation timeout
- Clear existing translations if they're no longer needed
ACL Configuration Issues
Make sure your ACL correctly identifies the inside addresses that should be translated. Use show access-lists to verify your ACL configuration and hit counters.
Interface Configuration
Verify that your interfaces are correctly configured as inside and outside using show ip nat statistics.
Dynamic NAT vs PAT
It's important to understand that dynamic NAT still uses a one-to-one mapping between inside and outside addresses. If you have more inside hosts than public IP addresses, some hosts may not be able to access the internet when the pool is exhausted.
For most scenarios with limited public IP addresses, PAT (Port Address Translation) or NAT Overload is more appropriate, as it allows multiple inside hosts to share a single public IP address using different port numbers. We'll cover PAT in a future tutorial.
Summary
Dynamic NAT provides automatic one-to-one mapping between private and public IP addresses using a pool of public addresses. Key points to remember:
- Define inside and outside interfaces
- Create an ACL to specify which inside addresses can be translated
- Define a pool of public IP addresses
- Configure the NAT translation rule
- Monitor pool usage to avoid exhaustion
Dynamic NAT is particularly useful in environments where you have more internal hosts than public IP addresses, but not all hosts need internet access simultaneously. In the next tutorial, we'll explore PAT (NAT Overload), which provides even more efficient use of public IP address space.