DoS TCP SYN Attack Mitigation
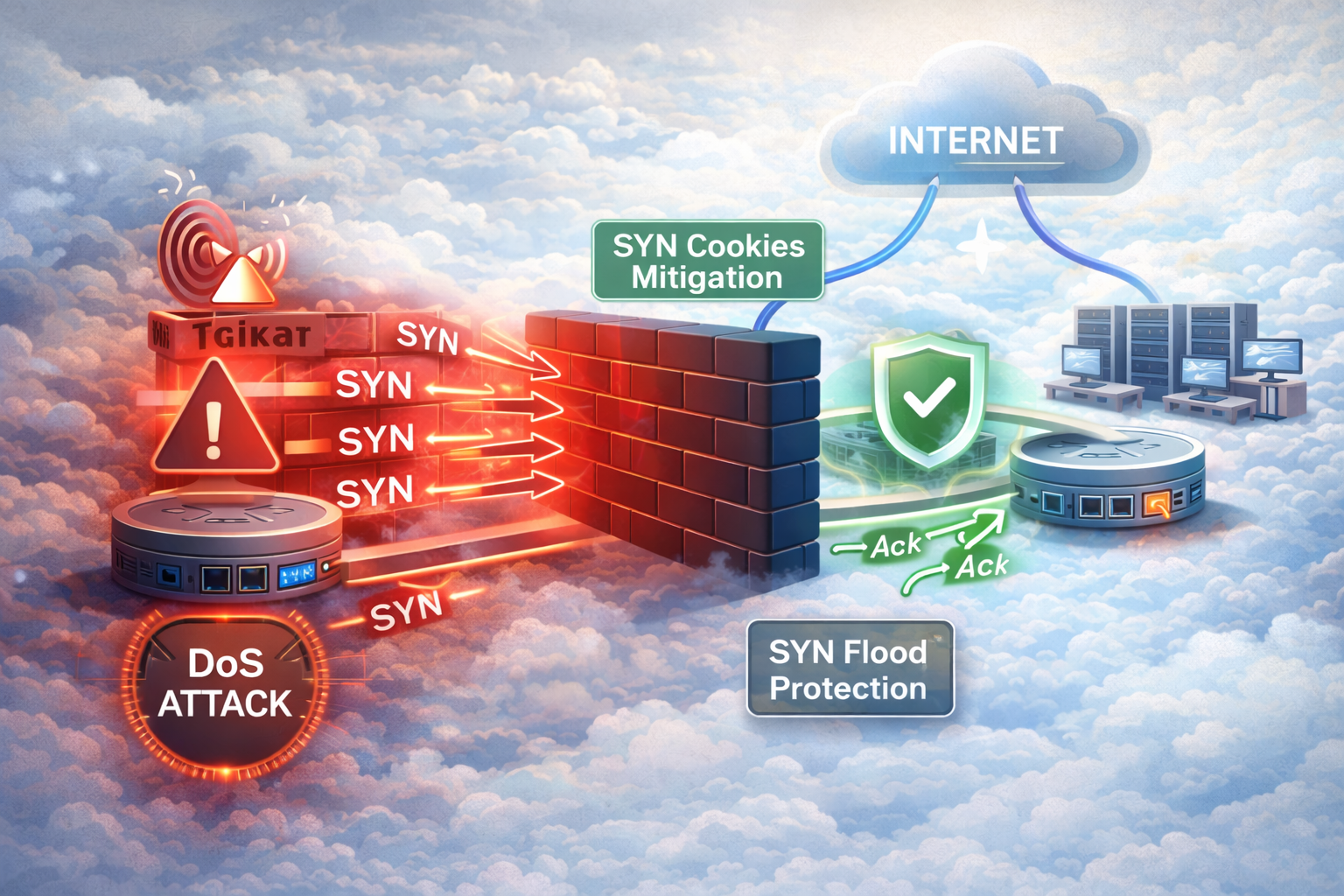
A DoS (Denial of Service) attack is an attempt to make a machine or network resource unavailable to its intended users. One common type of DoS attack is the TCP SYN flood attack, which exploits the TCP three-way handshake process.
Understanding TCP SYN Flood Attacks
In a normal TCP connection establishment, the client sends a SYN packet to the server, the server responds with a SYN-ACK packet, and the client completes the handshake with an ACK packet. During a TCP SYN flood attack, the attacker sends numerous SYN packets but never sends the final ACK, leaving the server with many half-open connections that consume resources.
Mitigation Techniques
1. TCP Intercept
Cisco routers can use TCP Intercept to protect servers from TCP SYN flood attacks. TCP Intercept can operate in two modes:
- Intercept Mode: The router intercepts TCP connection requests and establishes connections on behalf of the server
- Watch Mode: The router monitors connection attempts and drops suspicious connections
To configure TCP Intercept:
Router(config)# ip tcp intercept list 100
Router(config)# ip tcp intercept mode intercept
Router(config)# ip tcp intercept connection-timeout 30
Router(config)# access-list 100 permit tcp any host 192.168.1.10 eq 802. Rate Limiting
Configure rate limiting to control the number of connection attempts:
Router(config)# ip tcp intercept max-incomplete high 1000
Router(config)# ip tcp intercept max-incomplete low 800
Router(config)# ip tcp intercept one-minute high 500
Router(config)# ip tcp intercept one-minute low 4003. SYN Cookies
Enable SYN cookies on the server to handle SYN flood attacks:
Router(config)# ip tcp synwait-time 30
Router(config)# ip tcp selective-ack
Router(config)# ip tcp timestampMonitoring and Verification
Use these commands to monitor TCP Intercept statistics:
Router# show ip tcp intercept statistics
Router# show ip tcp intercept connections
Router# debug ip tcp interceptBest Practices
- Implement TCP Intercept on edge routers closest to potential attackers
- Use access lists to specify which servers to protect
- Configure appropriate timeout values based on your network requirements
- Monitor connection statistics regularly
- Consider using firewalls and intrusion detection systems for additional protection
Proper configuration of TCP SYN flood mitigation techniques can significantly improve your network's resilience against DoS attacks while maintaining legitimate traffic flow.