Hashing, What is it and how does it work?
Hashing, often referred to as a hash function, is a fundamental concept in computer science and cryptography. It's a mathematical algorithm that takes an input (or 'message') of any size and produces a fixed-size string of characters, which appears random. This output is called a hash value, hash code, or simply a hash.
Key Characteristics of Hash Functions
Deterministic: The same input will always produce the same hash output.
Fixed Output Size: Regardless of the input size, the hash output is always the same length.
Fast Computation: Hash functions are designed to be computed quickly.
Avalanche Effect: A small change in input produces a dramatically different output.
One-way Function: It should be computationally infeasible to reverse-engineer the original input from the hash.
Common Hash Functions
MD5 (Message Digest 5): Produces a 128-bit hash value, typically represented as a 32-character hexadecimal number. Though widely used, it's now considered cryptographically broken.
SHA-1 (Secure Hash Algorithm 1): Produces a 160-bit hash value. Also considered weak by today's standards.
SHA-256: Part of the SHA-2 family, produces a 256-bit hash. Currently considered secure and widely used.
SHA-3: The latest member of the Secure Hash Algorithm family, offering different output sizes.
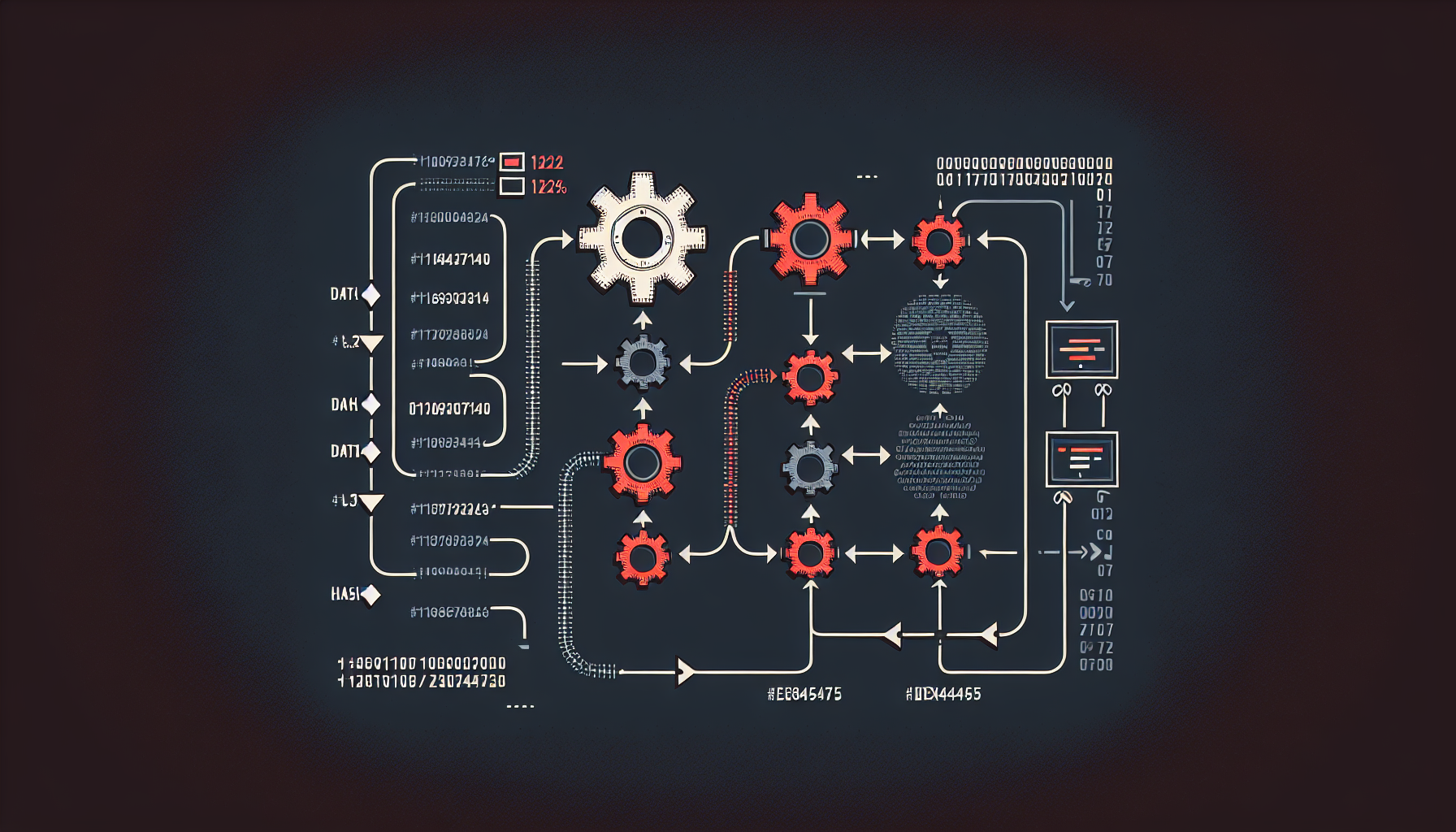
How Hash Functions Work
Hash functions use complex mathematical operations to transform input data. The process typically involves:
- Preprocessing: The input is padded and formatted to meet the algorithm's requirements.
- Processing: The formatted input is processed through multiple rounds of mathematical operations.
- Output: The final result is formatted as the hash value.
For example, if we hash the word "hello" using SHA-256:
Input: hello
SHA-256 Hash: 2cf24dba4f21d4288094c27b161de5f875e516a0ad7a9c8e03d3c2e66a61f01If we change just one character to "Hello":
Input: Hello
SHA-256 Hash: 185f8db32271fe25f561a6fc938b2e264306ec304eda518007d1764826381969Notice how completely different the hash values are, demonstrating the avalanche effect.
Applications of Hash Functions
Data Integrity: Hash values can verify that data hasn't been altered. If the hash of received data matches the original hash, the data is intact.
Password Storage: Instead of storing passwords in plain text, systems store their hash values. During login, the entered password is hashed and compared to the stored hash.
Digital Signatures: Hash functions are used in digital signature algorithms to ensure message authenticity.
Blockchain Technology: Hash functions are crucial in blockchain systems, linking blocks together and ensuring data integrity.
Hash Tables: In data structures, hash functions help create efficient lookup tables.
Checksums: File integrity verification uses hash functions to detect corruption or tampering.
Security Considerations
For cryptographic applications, hash functions must be resistant to:
Collision Attacks: Finding two different inputs that produce the same hash.
Preimage Attacks: Given a hash value, finding an input that produces that hash.
Second Preimage Attacks: Given an input and its hash, finding a different input that produces the same hash.
Practical Example: File Verification
When downloading software, you might see something like:
File: software.exe
SHA-256: 3b7e72f9c8a5d4e6f2a1b8c7d3e9f5a2b4c6d8e1f3a5b7c9d2e4f6a8b1c3d5e7After downloading, you can calculate the hash of your downloaded file. If it matches, the file is authentic and uncorrupted.
Limitations
While hash functions are powerful tools, they have limitations:
Hash Collisions: Though rare, different inputs can theoretically produce the same hash (pigeonhole principle).
Not Encryption: Hashing is one-way; it's not meant for data recovery like encryption.
Rainbow Table Attacks: Precomputed tables of hash values can potentially reverse simple hashes.
Hash functions are essential building blocks in modern computing, providing data integrity, security, and efficient data organization. Understanding how they work helps in making informed decisions about data security and system design.